Information Security Manager (CISM preparation course), CISM training, CISM course, CISM exam, CISM certification
Achieve global recognition in information security with the Information Security Manager (CISM®) certification and preparation course.
The Information Security Manager (CISM® preparation course) prepares you for one of the essential certifications for information security professionals who manage, implement, monitor, and evaluate information security in an organization. The course prepares Information Security managers for the performance of the function, including how to assess risks, implement effective governance and proactively respond to incidents.
This course addresses the themes of Information Security Governance, Information Security Risk Management, Information Security Program, Incident Management, allowing you to acquire knowledge also through discussion, exercises by domain, simulation exam, ensuring your preparation for the ISACA CISM certification exam.
Resources, themes, discussion, exercise by domain, simulation exam.
All to continue to maintain the 98% pass rate in ISACA exams!
Course program and training material updated in 2024.
This Training Plan and all associated documents are protected by Copyright and registered as a literary work at IGAC – Portugal.
Next GUARANTEED DATES 28-Aug-2024, Register now 23-Oct-2024, Register now
course evaluation 4.7 in 5
Information Security Manager (CISM preparation course), CISM training, CISM course, CISM exam, CISM certification
Introduction
This course is available to be delivered in a classroom and > Live Online Training <
This course is designed for managers and senior professionals in information security who intend to take the Certified Information Security Manager (CISM) examination. Recognized internationally, CISM certification is issued by the Information Systems Audit and Control Association (ISACA). The curriculum covers all the key domains addressed in the exam: Information Security Governance, Information Security Risk Management, Information Security Program, Incident Management.
Training Methodology
In this course the participants will revise the main concepts of information security management in accordance with the best practices of ISACA and the CISM certification domains, consolidate their knowledge through questions of exam preparation and in the end, perform a test simulation in order to assess the level of knowledge and the amount of effort needed to be aligned and to successfully pass the CISM certification exam.
This course is available to be delivered in a
> Live Online Training < model and classroom.
Live Training brings you the dynamic environment of the classroom, to your desk. Using your computer, you interact with the trainer and the trainees as if you were with them in the classroom.
Audience
Candidates and prospective candidates for the CISM examination and those wishing to expand their knowledge in the field of Information Security - they include:
- Information Security Managers/Professionals
- Security Directors
- Security Officers
- Security Consultants/Professionals
- Cybersecurity Managers/Professionals
- Executive and Operational Managers
Prerequisites
To participate in this course:
- Participants possess a basic knowledge about the different domains that will be addressed in the CISM exam. The course is an intensive review in preparation for the examination, not basic training.
- Participants must understand English since the course documentation is written in that language.
- Also, other requisites may apply, please check the quotation or the proposal received.
Duration (days)
3 days
Learning Objectives
At the end of the course students should be able to:
- Develop an information security governance structure aligned with organizational objectives.
- Establish and maintain a framework to provide assurance that information security strategies are aligned with business goals and objectives and consistent with applicable laws and regulations.
- Appropriately apply risk management principles and practices to an enterprise's information security program.
- Identify and manage information security risks to achieve business objectives.
- Develop and maintain an information security program, to implement the information security governance framework, that identifies, manages, and protects the organization’s assets while aligning to information security strategy and business goals, thereby supporting an effective security posture.
- Oversee and direct information security activities to execute the information security program.
- Establish an effective incident management program to respond to and subsequently manage incidents that threaten an enterprise's information systems and infrastructure.
- Develop and manage a capability to respond to and recover from disruptive and destructive information security events.
- Be prepared for the CISM® Certification exam based on the latest CISM Job Practice Areas (the certification domains)
Program
- Introduction and Course Plan
- Information Security Governance
- Information Security Risk Management
- Information Security Program
- Incident Management
- Exam Preparation: Simulation Exam
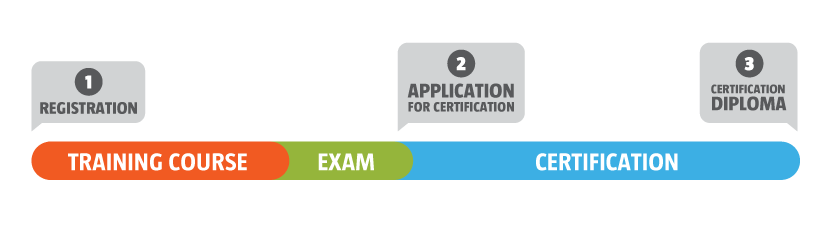
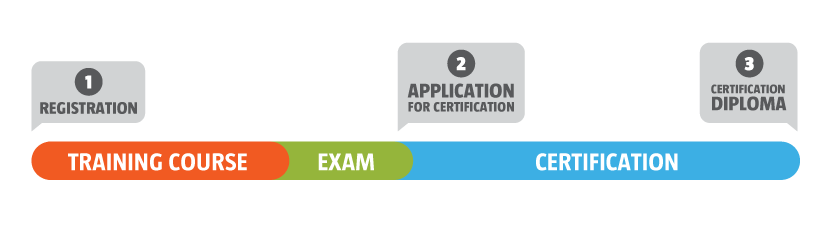
Exam
- The CISM exam is not included in the course price. Schedule your exam directly with ISACA. The exam is held at Behaviour or remotely using an ISACA proctor. After passing the exam successfully, you must submit your certification application on the ISACA website (www.isaca.org).
- CISM certification is based on a multiple-choice exam consisting of 150 multiple choice questions, about the 4 domains – Length: 4 hours. The passing mark is 450 on a scale from 200 to 800.
- For achieve the CISM Certification, candidates must pass the CISM exam and fulfill the remaining ISACA requirements.
Certification
This course prepares for the following exams:
Certified Information Security Manager (CISM®)
Trainer
Our specialists are consultants and auditors, with several years of experience in the areas of implementation, auditing and training in best practices, methodologies, standards and in the most recognized frameworks.
Some of our experts work directly in the improvement of these frameworks, methodologies, and standards through its participation in the technical committees, as members or taking distinct roles in the major organizations worldwide, working and supporting the best practices communities. Our team of instructors are ISACA certified, holding the CISA, CISM, CGEIT, CRISC and COBIT certifications, (ISC)2 certified, holding CISSP certification and others from the most recognized worldwide, as PMP, ISO/IEC 27001, ISO/IEC 27005, ISO 31000, ISO 22301, among others.
General Information
- Training in English language.
- Online training material resources in English, with online access, and in accordance with the commercial conditions.
- Practical step-by-step implementation methodology
- Behaviour Digital Participation Certificate of 24 CPD/CPE credits.
- Online Certification Exam in Portuguese or English language. The exam can be taken up to 2 months from the start date of the course.
- If the candidate fails the exam, he is entitled to one free retake within a 2 month period from the date of the exam result.
- Certification Diploma and certification badge after successful examination and formal process registration. This process has no associated cost.
Benefits
- Information Security Manager (CISM® preparation course) is oriented towards the acquisition of knowledge of the ISACA CISM Job Practice Areas.
- Gain of working knowledge of Information Security Management.
- Empowers employees with a universal language, circumventing ambiguity with industry-accepted terms and practices.
- Fulfills government and organization requirements for information security management certification mandates.
- Provides increased credibility for your organization, when working with vendors and contractors, and satisfies certification mandated requirements for service providers and subcontractors.
- Behaviour Pedagogical Model aims to provide a learning environment conducive to acquisition of competences, in accordance with objectives of each training program. Promoting interaction, participation and appreciation of experiences, we contribute to meaningful learning, certification and international recognition but, above all to the development of critical thinking and autonomy.
- Behaviour is an organization accredited by DGERT (Portuguese Government Entity) and has its Quality Management System (QMS) implemented in accordance with the requirements of ISO 9001, the requirements of DGERT, the requirements of the European standard NP 4512 and the standard ISO 10015.
Dates and Price
Click on “Price and Registration” to access more information and also the price:
Guaranteed Dates Program
(*) All dates of this course are guaranteed only for the events that take place in Lisbon. In other physical locations or in Live Online training, all events are subject to a minimum number of participants.
On Behaviour all classroom courses at Lisbon occur regardless of the number of trainees in room. The concept of setting up classes does not exist in our classroom educational model, which is why all classroom public dates, presented on the website, are guaranteed. So if you're in Portugal or anywhere else in the world, you can prepare your week and your trip, as long as you ensure your registration in the a classroom course.
Volume Discounts
For companies, Behaviour offer discounts, starting from the registration of the 2nd participant, in the same course and on the same date.
Simulate the prices for the number of participants you want to register to
training@behaviour-group.com or contact us via chat.
Hotels and Useful Information
Know where you can stay in Lisbon.
For more information please check online Booking.com